Cybersecurity
Cybersecurity can be confusing and overwhelming, but it is essential for every business. At CTS, we’ve developed a proven and cost-effective cybersecurity strategy for any business that actually works!
As seen in the news every single day… cyber attacks are real and they are only going to increase as artificial intelligence (AI) enables the malicious actors to create more sophisticated attacks. And the worst part is that they are specifically targeting small and midsized businesses (SMBs) knowing that their cyber defenses may not be ready for the daily assault.
All organizations need to have a comprehensive cybersecurity plan and it NEEDS to be more than just a “good” firewall and anti-virus. Most businesses are not sure what solutions are needed or what level of protection they need, because there are other factors that play into these decisions, such as budgets. CTS has effective cybersecurity solutions that are designed for every business regardless of industry or resources.
Some of our proven cybersecurity solutions are:
- Endpoint Detection and Response (EDR)
- Security Operations Center (SOC)
- Managed Extended Detection and Response (MXDR)
- Threat Detection for all systems, including Microsoft 365 and other cloud solutions
- Written incident response procedure and testing
- Dark Web Monitoring
- Security Awareness Training
Contact us today for a free 30 minute security discussion and assessment!
Seeking cybersecurity tips for your business? Download our Top 6 Cybersecurity Solutions for Every Business whitepaper.
Consider the following statistics when thinking about whether you need Cybersecurity protection for your business:
- An average of 2,244 cybersecurity attacks occur each day according to a study by the University of Maryland.
- Blackberry reports that the United States remains the most highly targeted country with 65% of all cyberattacks targeting Americans.
- According to Cybersecurity Ventures, over 50% of all cyberattacks target small to medium sized businesses (SMBs).
- Aside from costs a business may need to pay those behind a Cybersecurity attack to get their data back, there are other significant costs a business may incur:
- Between the 1st quarter of 2020 and the 3rd quarter of 2021, Statista reported that the average duration of downtime after a ransomware attack increased from 15 to 22 days.
- A survey conducted by PricewaterhouseCoopers found that 87% of consumers consider changing who they conduct business with when a cyberattack occurs.
- Over 60% of SMBs that encounter a cyberattack, go out of business within 6 months according to Cybersecurity Ventures.
Can your business afford to take a chance on not having proper Cybersecurity protection in place?
If still unsure, consider the following example:
- Business XYZ has 30 employees whose average annual salary and benefits package is $58,500 per employee, monthly operating and marketing costs of $6,500, and $4.8 million in gross sales. If this business encounters a Cybersecurity attack and loses just one day of business as a result, the cost is estimated to be at least $27,023! As previously shared, customer trust and their business reputation are also likely jeopardized, and this is at a cost that could be indefinite.
At Computing Technology Solutions (CTS), we support a diverse number of businesses by being their Cybersecurity partner. We perform a risk assessment with every new client that allows us to help understand where they have exposure to potential attackers. With this assessment and our comprehensive security stack, we implement solutions that match the needs of each business.
To learn more about CTS becoming your Cybersecurity Partner, contact Frank Stephens at [email protected] or 1.888.7.CTSNOW.
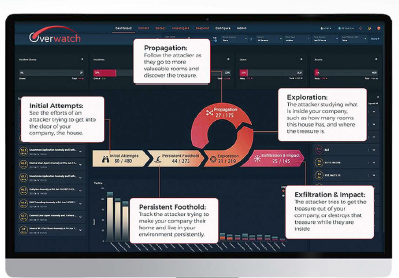
What is Open MXDR?
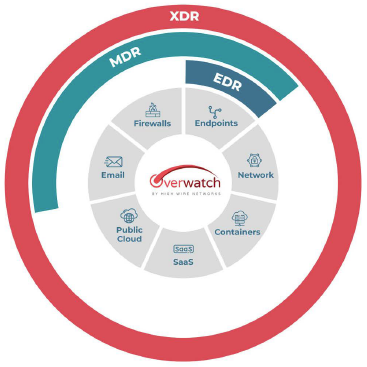
Managed Extended Detection and Response (MXDR) is a vendor-agnostic XDR solution that consolidates multiple security products into a single platform to better correlate, detect, and respond to threats. This centralized platform empowers security teams to identify threats and breaches and provides context around incidents that can bolster and speed up response and remediation quicker and easier.
The CTS MXDR delivers powerful open extended detection and response (Open XDR) for end-to-end cybersecurity solutions. Cybercrime is rampant and businesses are demanding more from their security providers. Cloud adoption and work from home or anywhere – on any device – are blurring infrastructure boundaries and creating an ever-expanding surface for cyberattacks. CTS MXDR condenses the entire surface into an intelligent, manageable stream for more robust security, better threat identification and faster responses.
CTS MXDR is a turnkey solution built from best-in-class technologies and a best practices security framework from the CTS Cybersecurity team. It’s an integral part of our managed cybersecurity services suite, delivering Al-powered Open XDR solutions from our market-leading team and tools in our 24/7 Security Operations Center (SOC).
CTS MXDR Platform Features
- Comprehensive, automatic sensor-based data collection
- Physical (on-premises) and cloud visibility
- Integrated IDS/IPS paired with Al to reduce false positives
- 50,000+ detections for known and unknown behaviors mapped to the cybersecurity kill chain
- Advanced analytics and data-lake mining
- Built-in event-response and case-management capabilities
- Monthly reporting on activities
Benefits of CTS MXDR
Security Benefits
- Protects your entire attack surface
- Enhances existing infrastructure with superpowered Al
- Delivers best-in-class intelligence regardless of existing security products and services
- Deploys across network, cloud and endpoint infrastructure
- Generates exponential improvements in detection [MTTD) & response [MTTR) times
- Developed and delivered by CTS’ market-leading SOC team
Cost Benefits
- Leverages existing infrastructure
- Fewer incidents to manage and recover from
- Faster recovery time
- Expandable and extensible in vendor-agnostic fashion
- Streamlined sourcing and ops
Benefits of CTS MXDR + SOC
- Rapid Detection + Response: System automates data correlation, reducing false positives and alert fatigue so analysts can respond without delay
- Expertly Trained Security Analysts: Our analysts are trained experts in their field, which decreases mean time to recognition and action
- Reduction in Breach Risks: Faster detection and action reduces the overall risk of a breach, allowing containment
- User Management: We leverage behavior analysis, active directory monitoring, hostile network attacks, Microsoft 365, G-suite integration and more
- Network + Infrastructure Monitoring + Protection: We use encrypted log storage, intelligence feeds, real-time automated remediation and asset discovery, API attacks and Zero-day protection
- Compliance Support: We provide policy templates, incident response management, compliance reports and documents, and auditor report access
- Alignment with Industry Frameworks: Immediate alignment with defense-in-depth strategies and a balanced response through industry recognized standards like NIST, CIS, CMMC, MITRE, HIPAA, and ISO
We're Here To Help!
Office
2033 N. Milwaukee Ave, Suite 351
Riverwoods, IL 60015